You don't need a 50-person SOC to stop enterprise-grade threats. You need the right platform.
Commercial businesses today face the same ransomware, cloud breaches, and multivector attacks that Fortune 500 companies do. The difference is the resources available to fight back. According to the 2026 Unit 42 Global Incident Response Report, the fastest attacks now go from initial access to exfiltration in just 72 minutes — 4x faster than the year before. And in nearly 90% of investigations, attackers didn't break in. They logged in.
That's the threat landscape your team is walking into every day. If you're running a lean IT or security team, you already know this pressure. The alerts pile up. The context is missing. And the expectation to respond like a full SOC hasn't gone away.
Cortex XDR was built for exactly this situation.
Stop Threats Before They Start
The first job of any security platform is prevention, and Cortex XDR takes a prevention-first approach that works out of the box, no custom tuning required. In the 2025 SE Labs Ransomware test, it achieved 100% prevention. In the MITRE ATT&CK Round 6 Evaluations, it delivered 100% detection accuracy with zero prevention false positives.
That matters for lean teams because every false positive is time you don't have. Ultimately, the most effective way to manage a security crisis is to ensure it never becomes one; prioritizing prevention over reaction keeps your team focused on growth rather than damage control.
Cortex XDR layers its defenses across three stages:
- Pre-execution: Static analysis uses machine learning to analyze thousands of file attributes and block never-before-seen zero-day threats before they ever run.
- During execution: Exploit prevention monitors key endpoint processes and blocks attacker techniques in real time, even when a patch isn't yet available.
- Post-execution: Behavioral threat protection monitors active system patterns to catch fileless attacks, suspicious user activity, and lateral movement, terminating threats mid-attack.
This multilayered architecture means your team isn't scrambling to cover gaps between tools. One platform handles the full attack lifecycle:
Turn Alert Noise Into Actionable Incidents
Alert fatigue is one of the biggest drains on security teams. When thousands of disconnected, low-context events hit your queue every day, critical threats get buried. Cortex XDR solves this by automatically stitching disparate data points into a single causality chain.
That chain tells the full story of an attack: how it started, which files were touched, and where it tried to go. Instead of hunting across multiple consoles to piece together what happened, your analysts see a complete, prioritized incident with the who, what, and how already answered.
The result: Cortex XDR eliminates up to 99.6% of alert noise
For a SOC analyst, that means:
- Fewer manual tasks and less time chasing context across tools
- High-confidence incidents that are ready to act on, not just review
- The ability to perform deep forensic analysis without needing specialized expertise for every alert
For managers, it means your team focuses on validated threats rather than noise, making every hour of analyst time count more.
Respond Fast, With or Without a Full Team
Speed matters when an attack is in progress. The longer a threat stays active, the greater the damage and the longer the recovery. Cortex XDR gives your team the full attack context needed to move decisively, and then automates as much of the response as possible.
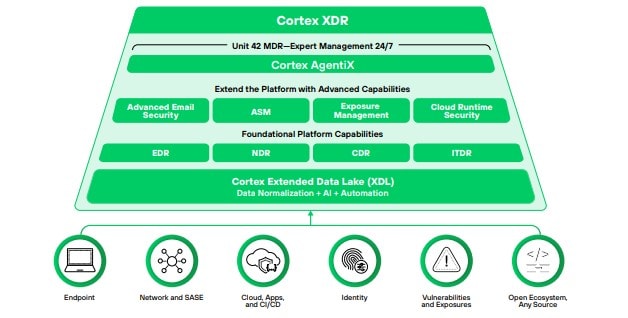
Over 100 built-in playbooks from Cortex XSOAR handle immediate containment with minimal human intervention. Cortex AgentiX, a workforce of AI agents, autonomously handles triage, enrichment, and containment at machine speed. And every automated action comes with a clear explanation, so your team understands exactly what happened and why.
For organizations without 24/7 in-house coverage, Cortex XDR pairs with Unit 42 Managed Detection and Response (MDR). This adds expert threat hunters directly into your operations as an extension of your team, providing:
- 24/7 monitoring and alert management
- Proactive threat hunting with high-fidelity Unit 42 threat intelligence
- Decisive remediation in minutes, not hours
- Executive-ready reports to communicate security posture to leadership
Your staff focuses on the business. Elite analysts handle the threats.
A Platform That Grows With You
One of the practical advantages of Cortex XDR is that it doesn't require you to rip and replace your existing infrastructure. It deploys alongside your current tools and scales as your needs evolve.
Start with core endpoint protection and add data sources over time, whether that's cloud workloads, identity management, network detection, or advanced email security. The licensing model reflects this flexibility:
- XDR Pro (per endpoint): A comprehensive starting point for organizations looking for the visibility and integration needed to scale their defenses. Ideal for teams who want direct control over their environment.
- XDR + Unit 42 MDR: Built for organizations without in-house security, providing 24/7 expert-led coverage without the cost of hiring a full security team.
Both tiers include endpoint threat prevention, behavioral detection, automated response, and unified case management with risk scoring. Advanced capabilities like cloud runtime security, identity threat detection, and attack surface management are available as add-ons when you're ready to expand.
The Bottom Line
Your businesses can't afford to keep throwing headcount at a threat landscape that moves faster every year. Cortex XDR gives lean teams the prevention, detection, and response capabilities of an enterprise SOC without the complexity, cost, or constant manual overhead.
The threats targeting your organization are sophisticated. Your platform should be too.
Download our At-a-Glance one-pager and more comprehensive Solution Brief today!