When a novel EDR bypass drops on GitHub, or a critical CVE hits the CISA KEV catalog, the security teams don’t just need to know it exists. They need the answer to one immediate question: “Does our Cortex XDR detect this right now?”
Historically, answering that question was a race against the clock. My research team would spend hours manually reading deep-dive blogs, extracting complex techniques, reverse-engineering newly published proofs-of-concept (PoCs), and manually validating our existing detection coverage. But by the time a human security researcher finds a new technique, triages it, checks whether the product detects it, and writes up a coverage, dozens more threats have landed.
We realized that to stay ahead of rapidly evolving threats, we needed an autonomous solution. We needed a system that could generate a personalized, trendy, and highly prioritized threat intelligence (TI) feed specifically tailored to our Cortex product’s detection posture.
The Solution: Autonomous AI Threat Intelligence
To close the time gap between a threat emerging and our product defending against it, we built a custom autonomous threat intelligence AI agent.
Instead of generic alerts or noisy lists of CVEs, this agent operates as a digital extension of our research team. It continuously ingests unstructured threat data from across the web, analyzes the underlying malicious techniques using LLM, and most importantly, autonomously extracts and maps the exact primitives, TTPs, and PoCs that our researchers need to validate coverage.
We aren’t just using generative AI to summarize text. We are using it to combine the deep, low-level expertise of our human researchers with machine speed to drastically reduce our time-to-detection. By automating the most critical parts of threat hunting, identifying emerging, high-impact exploits, and breaking down their technical mechanics, the agent feeds our team with a highly customized intelligence pipeline. Instead of wasting hours searching for technical details, our researchers can instantly focus on analyzing our defenses, closing coverage gaps, and delivering proactive remediation to our customers.
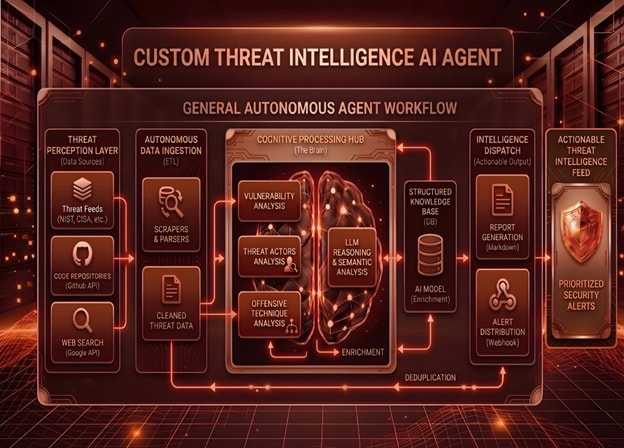
Deconstructing the Agent Architecture
To understand how this agent works, let's break down the autonomous workflow into its core building blocks. Just as a human security analyst does, the agent needs to perceive information, process it, remember it, and finally, act on it.
Threat Perception Layer
Acting as our digital scout, this layer leverages external APIs to continuously monitor the threat landscape. It polls structured threat feeds (such as CISA and NIST), scans unstructured code repositories (such as GitHub) for newly published proof-of-concept (PoC) exploits, and utilizes web search APIs to gather broader context on breaking security news.
Autonomous Data Ingestion
Raw data from the internet is messy. This layer acts as the translator, taking unstructured HTML, JSON blobs, and API responses and running them through dedicated scrapers and parsers. The goal is to extract only the relevant signals, strip away the noise, and output clean, standardized threat data that the AI can analyze without hallucinating.
Cognitive Processing Hub
This is the core engine (“The Brain”) of the agent. Here, an LLM is used not as a chatbot, but as a reasoning engine. Operating with schema-constrained prompts written from the perspective of a security researcher, it extracts offensive techniques, profiles potential threat actors, and analyzes vulnerability severity.
Structured Knowledge Base
An intelligent agent needs persistent memory to remember what it has already seen. The agent uses a MongoDB as its memory, storing all previously processed intelligence. This allows it to cross-reference new data against historical threats, leveraging semantic deduplication so that a single technique reported across three different blogs becomes a single clean unified entry.
Intelligence Dispatch
Once the brain synthesizes the intelligence, this layer formats and routes the findings. It automatically generates structured Markdown reports and triggers distributions via webhooks, including daily Slack reports and monthly deep-dives. It meets our researchers where they already work.
Actionable Threat Intelligence Feed
Instead of thousands of raw CVEs and noisy links, the end product is a highly curated, prioritized feed of security alerts. It gives our teams the bottom line: the exact threat, how the exploit works, and the precise actionable data needed to evaluate our current Cortex detection coverage.
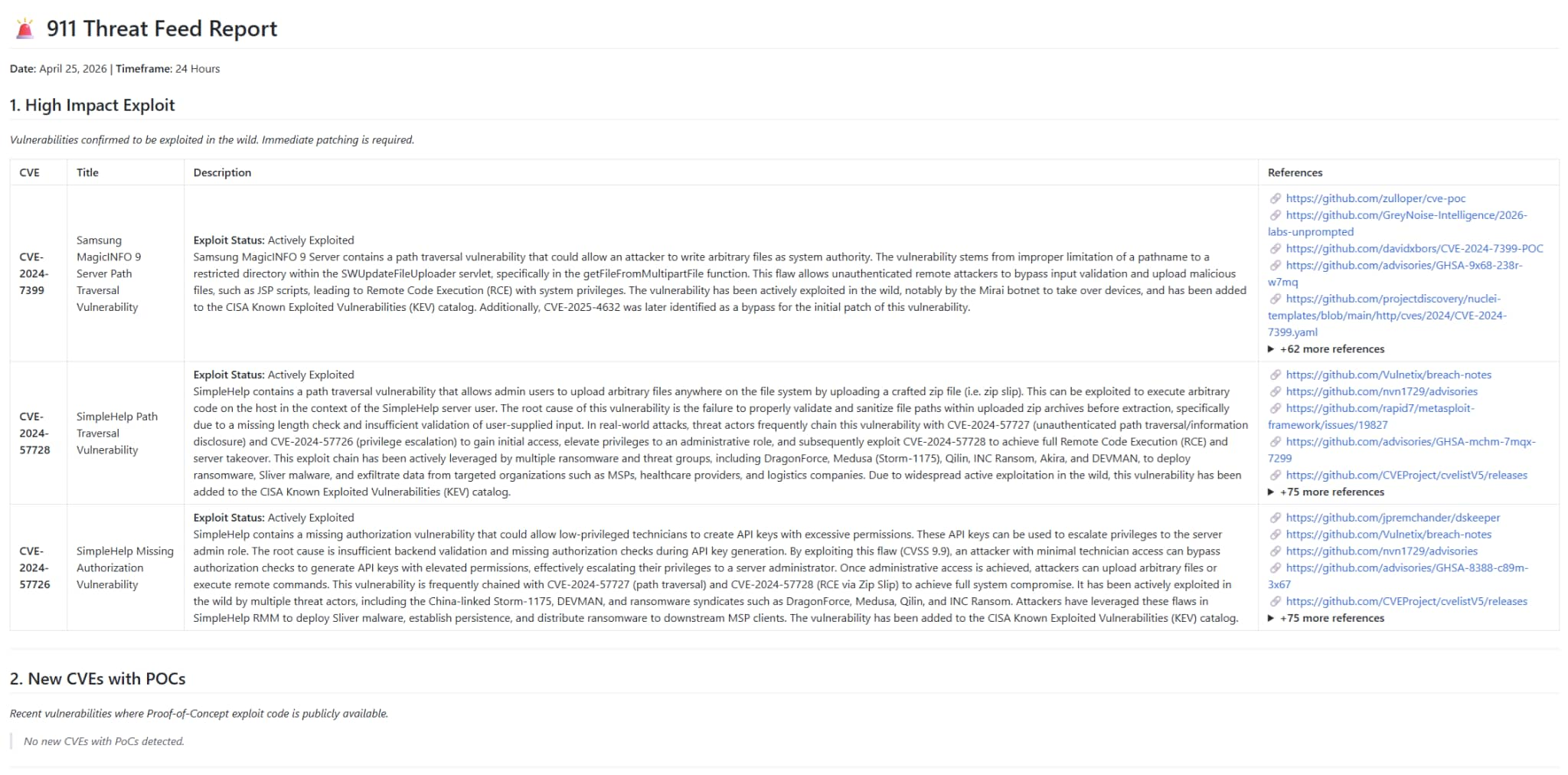
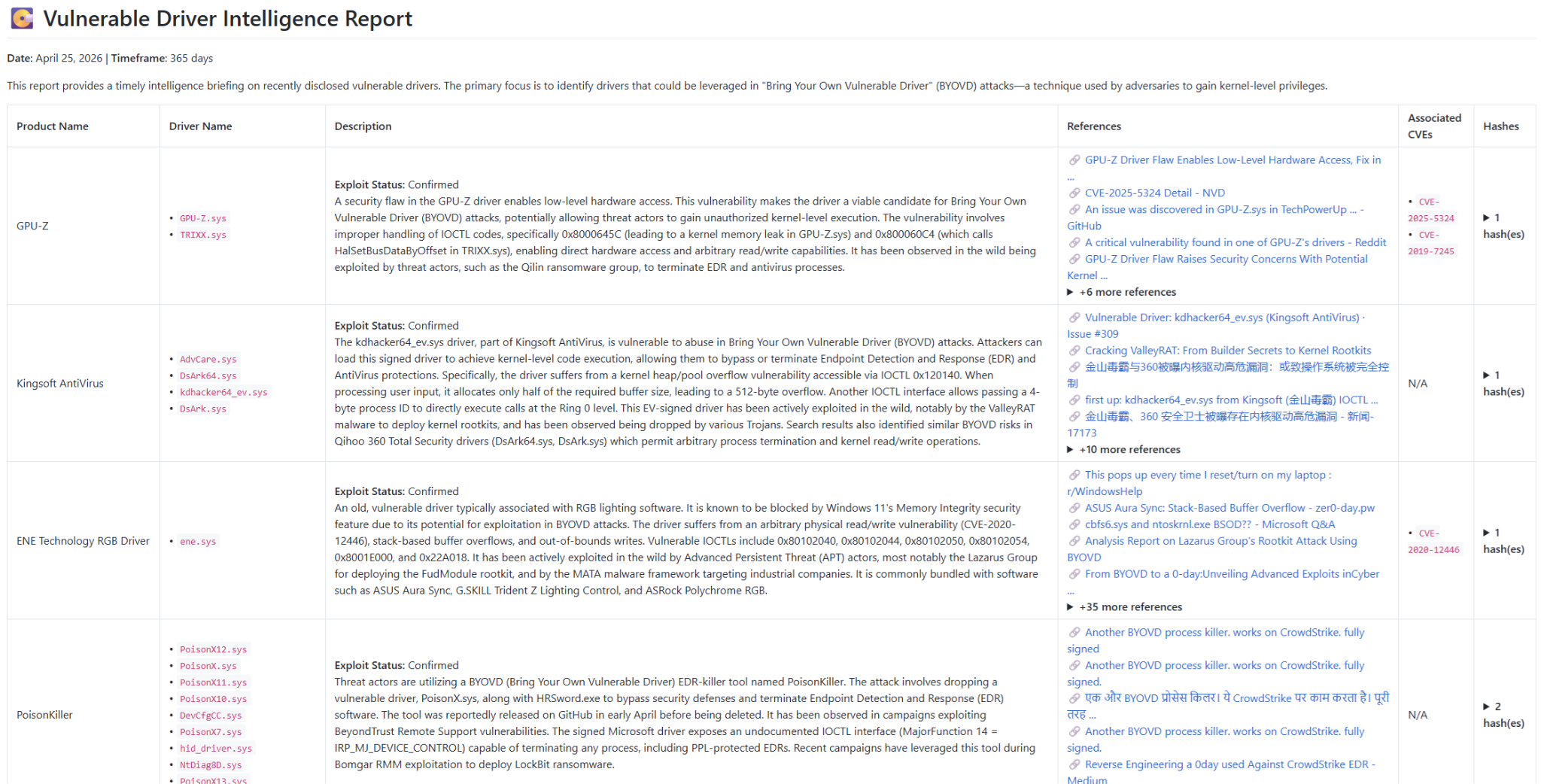
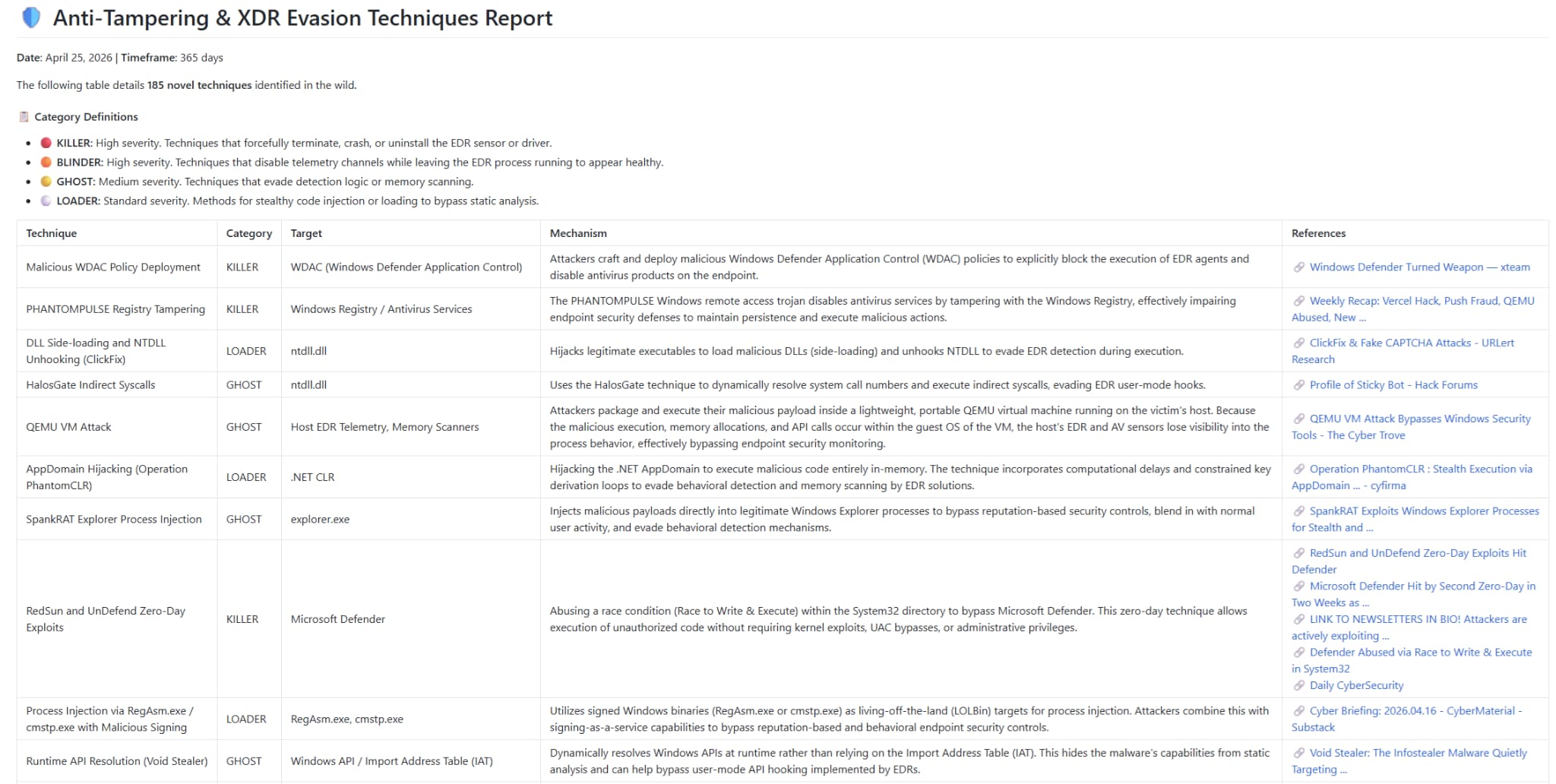
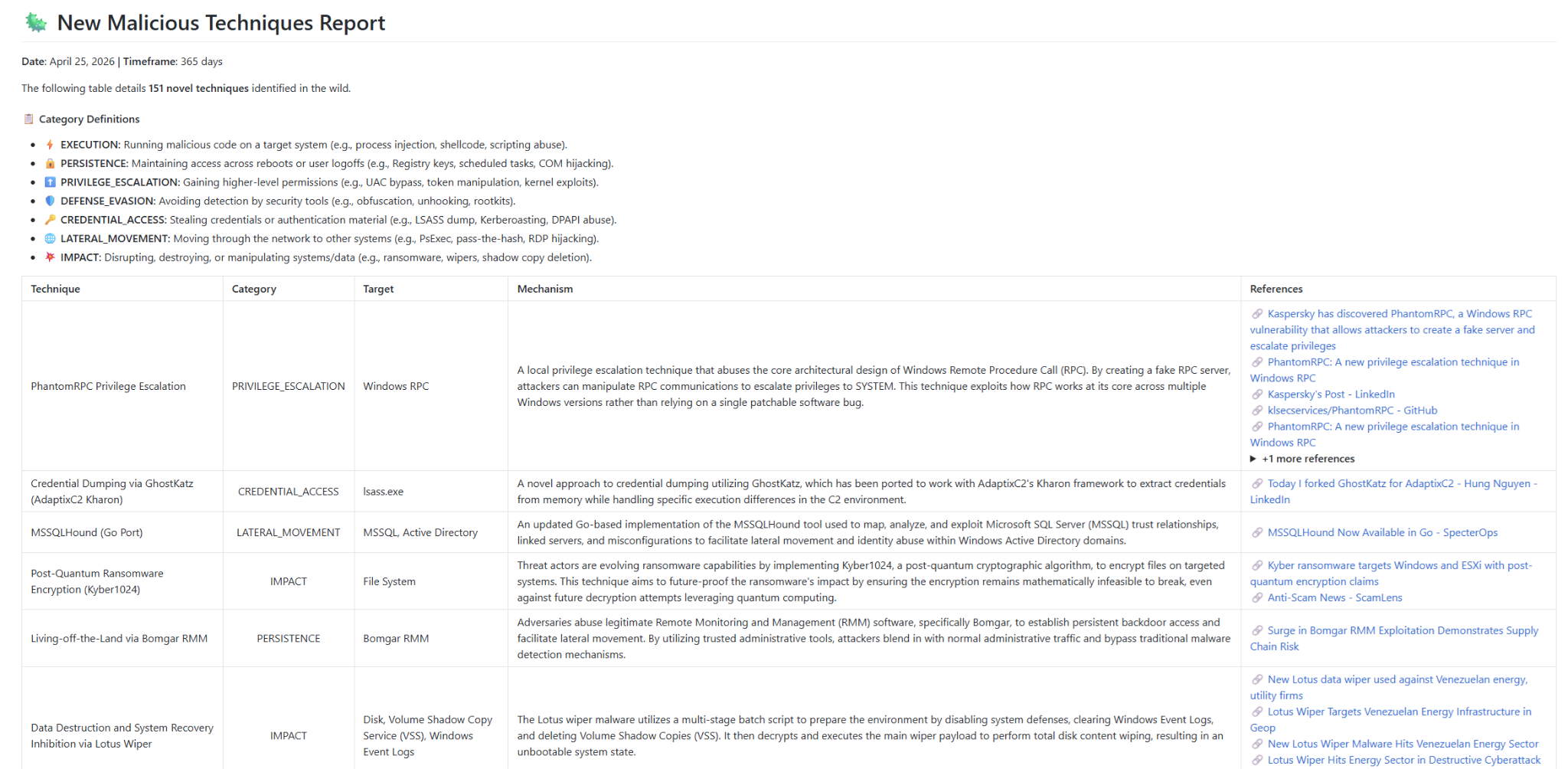
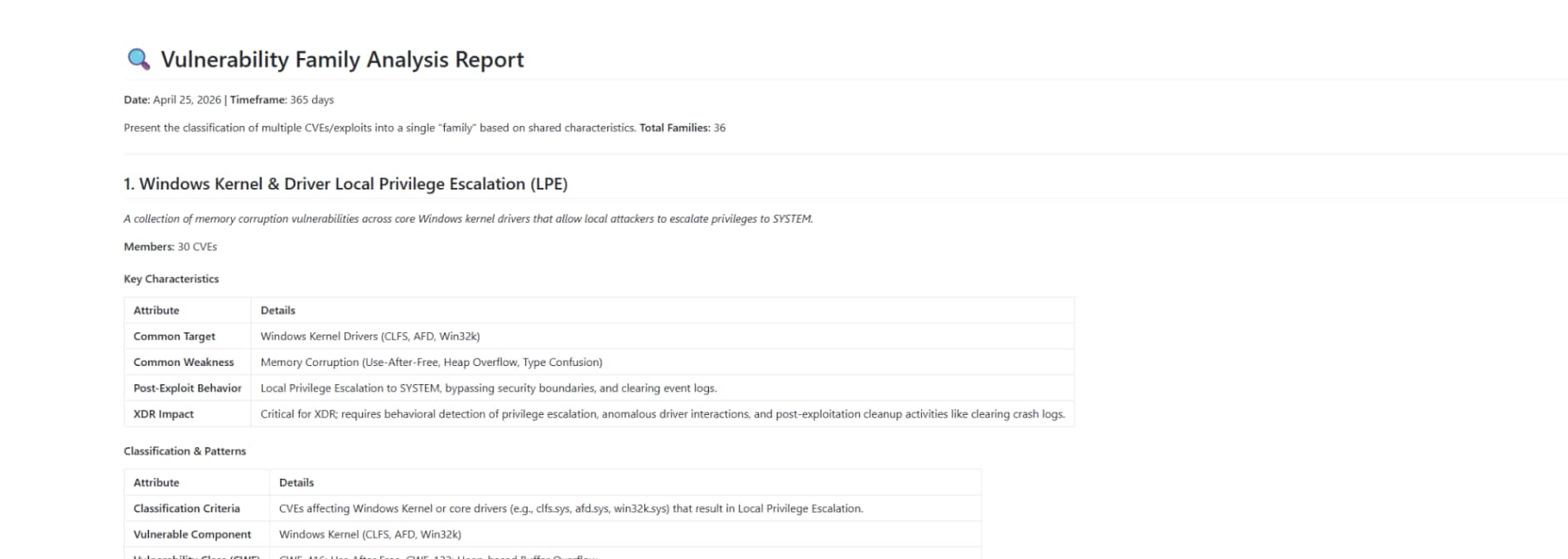
Below are some examples of curated reports customized to the needs of the team:
The Future of Autonomous Threat Hunting
The days of manually refreshing feeds and drowning in noisy CVE lists are ending. By combining traditional data scraping with the reasoning power of modern LLMs and the deep technical expertise of our researchers, we are building custom intelligence pipelines that scale our capabilities infinitely.
In the AI era, resilience is an architectural choice. With autonomous tools like this, we are ensuring that Palo Alto Networks remains a step ahead of the adversary, translating technical threat data into real-time, actionable defense.
To learn more about this and other agentic AI agents available in Cortex, reach out to a Palo Alto Networks representative today for a demo.