What is Zero Trust Network Access (ZTNA) 2.0
ZTNA 2.0
Zero Trust Network Access 2.0 overcomes the limitations of legacy ZTNA solutions, providing secure connections to deliver better security outcomes for businesses with hybrid workforces.
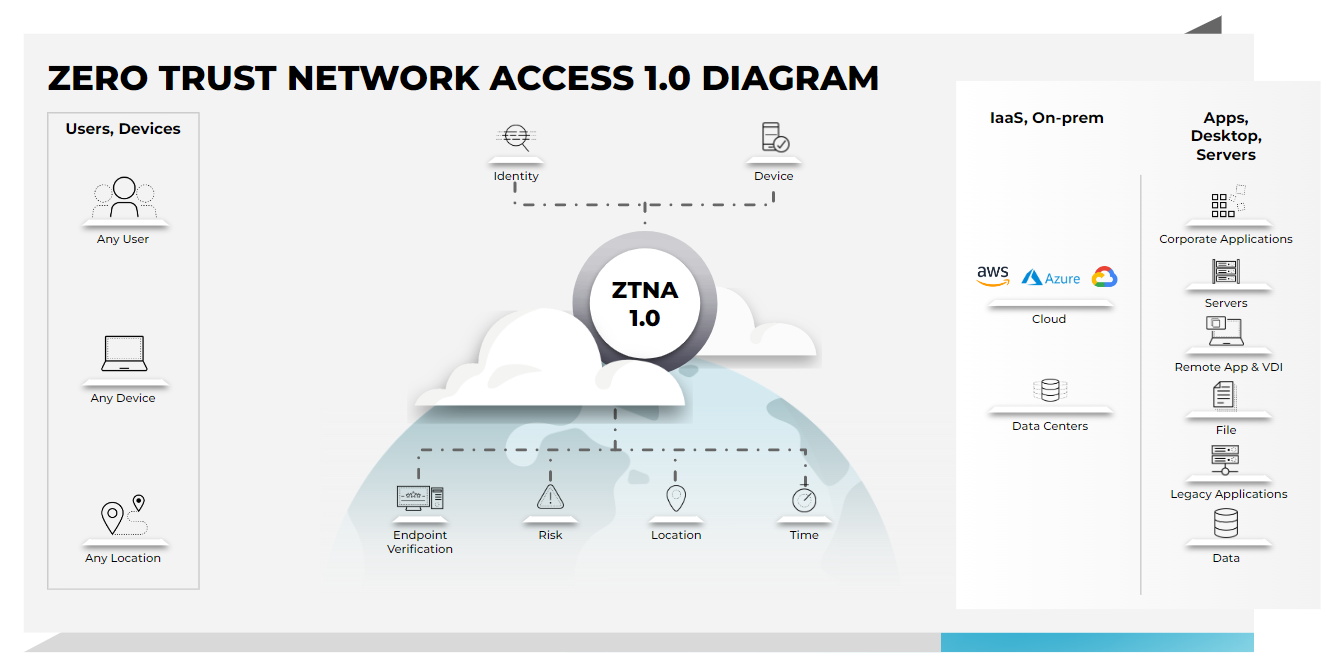
Current ZTNA 1.0 (or legacy) approaches support only coarse-grained access controls, incorporate an “allow and ignore” approach for both users and app traffic, and provide either little or no advanced security consistently across all apps – including rudimentary data loss prevention (DLP) – which violates the principle of least-privileged access and exposes organizations to increased risk of a breach.
ZTNA 1.0 vs. ZTNA 2.0
The biggest shift seen in networking and security over the past 24 months has been that work is no longer a place we go to but rather an activity we perform. Hybrid work is our new normal, which means our apps and users are now everywhere and anywhere, dramatically increasing our attack surface. In parallel, we’ve also seen an increase in the sophistication and volume of cyberattacks attempting to take advantage of this massively increased attack surface.
Current ZTNA 1.0 solutions only solve some of the problems associated with direct-to-app access. In particular, ZTNA 1.0 solutions:
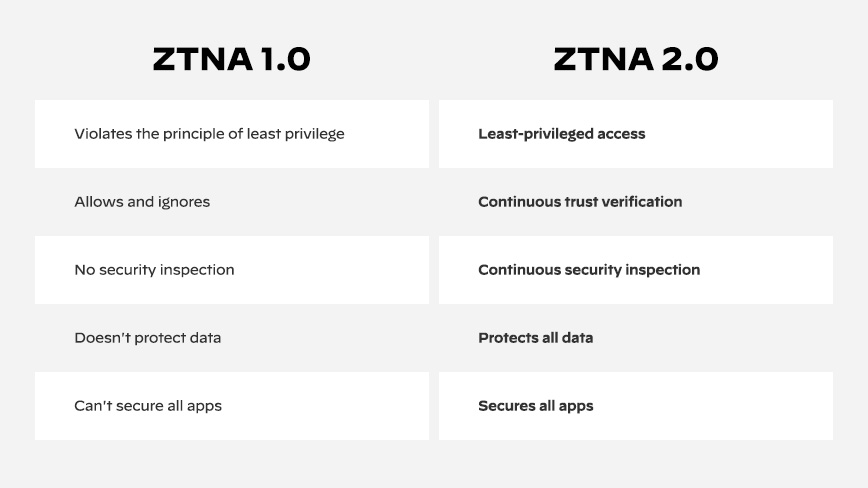
- Violate the principle of least privilege. ZTNA 1.0 approaches identify applications based on coarse-grained network constructs like IP address (or FQDN) and port number. This presents three key problems that violate the principle of least privilege:
- If an app uses dynamic ports or IP addresses, access is therefore granted to broad ranges of IPs and ports, exposing more surface area than necessary.
- Access cannot be restricted at the sub-app level or app function level; access can only be granted to entire apps.
- Any malware that listens on the same allowed IP addresses and port numbers is able to freely communicate and spread laterally.
- Operate on the allow and ignore model. All ZTNA 1.0 solutions follow this basic principle: once access to an app is granted, that communication is implicitly trusted forever; 100% of breaches occur on allowed activity, which an “allow and ignore” approach cannot prevent.
- Do not provide security inspection. ZTNA 1.0 solutions assume all allowed traffic is free from malware and other threats or vulnerabilities as they have no ability to detect or prevent malware or lateral movement across connections.
- Do not protect data. With ZTNA 1.0, there is no visibility or control of data, exposing the enterprise to the risk of data exfiltration from attackers or malicious insiders.
- Cannot secure all applications. ZTNA 1.0 offerings cannot properly secure microservices-based cloud native apps, apps that use dynamic ports like voice and video apps, or -initiated apps like helpdesk and patching systems. Moreover, ZTNA 1.0 solutions completely ignore SaaS apps, which now represent the majority of enterprise apps.
In addition to the capabilities that ZTNA 1.0 solutions lack, next-generation ZTNA solutions also miss the mark to fully protect your users, apps and data.
Next-Gen ZTNA vs. ZTNA 2.0
There are solutions out there that claim to be next-gen ZTNA solutions. However, they still have the same shortcomings as ZTNA 1.0, such as allow and ignore, violating least privilege, and a lack of consistent security and data protection for all apps. Clearly what is needed is a paradigm shift in securing direct-to-app access in today’s hybrid work and cloud-first world.
ZTNA 2.0 Benefits
To try and get a handle on the exploding attack surface and regain control, ZTNA has emerged as the preferred way to reduce the attack surface by providing the least-privileged direct-to-app access required by today’s hybrid workforce. Spurred on by the urgent need to replace legacy and outdated VPN deployments that backhaul traffic and provide network or LAN access, these initial ZTNA, or 1.0, solutions fail to deliver on the promise of Zero Trust as evidenced by significant limitations in current 1.0 solutions. It is clear a new approach is needed, and that new approach is ZTNA 2.0.
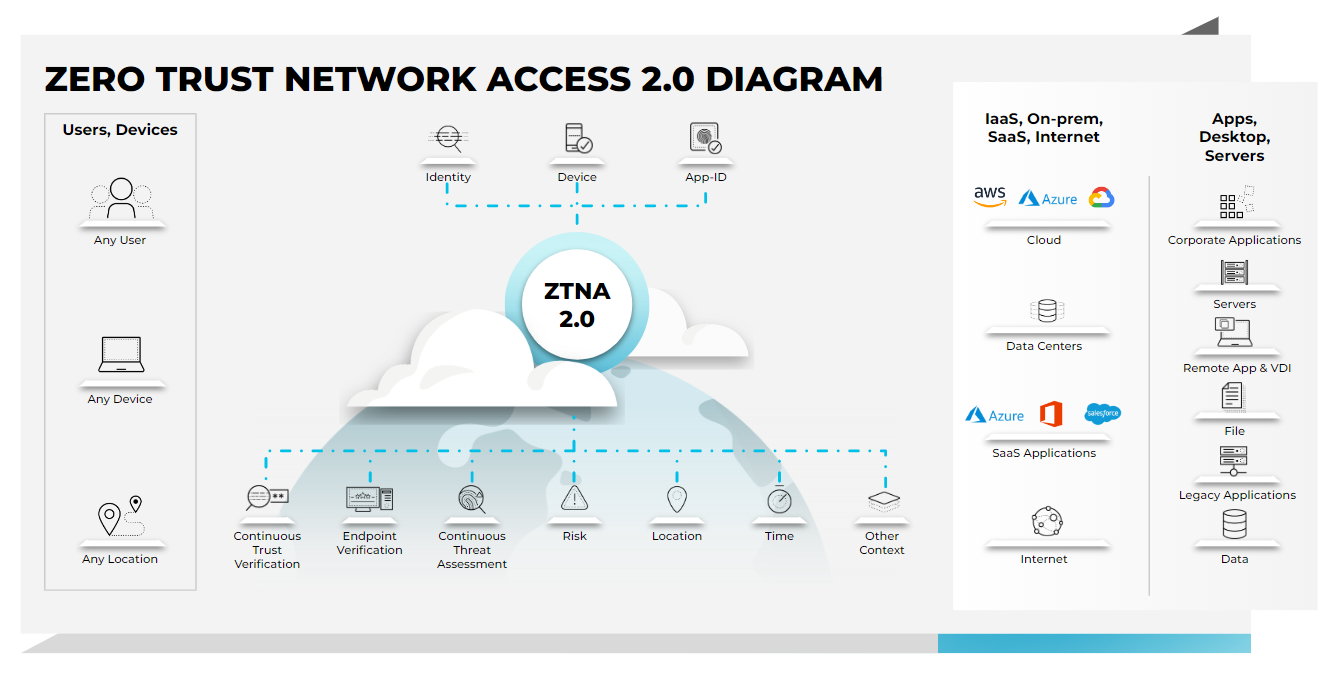
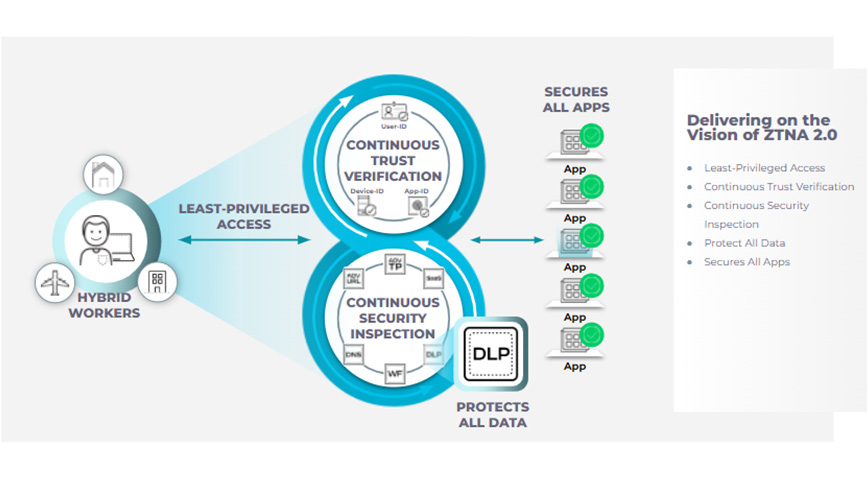
ZTNA 2.0 overcomes the limitation of ZTNA 1.0 and delivers on the promise of a true Zero Trust architecture. To effectively solve the shortcomings of ZTNA 1.0 approaches, ZTNA 2.0 is purpose-built to deliver:
- True least-privileged access: Identify applications based on App-IDs at Layer 7. This enables precise access control at the app and sub-app levels, independent of network constructs like IP and port numbers.
- Continuous trust verification: Once access to an app is granted, trust is continually assessed based on changes in device posture, user behavior and app behavior. If any suspicious behavior is detected, access can be revoked in real time.
- Continuous security inspection: Employ deep and ongoing inspection of all traffic, even for allowed connections to prevent all threats, including zero-day threats. This is especially important in scenarios where legitimate user credentials are stolen and used to launch attacks against applications or infrastructure.
- Protect all data: Apply consistent control of data across all apps used in the enterprise, including private apps and SaaS, with a single DLP policy.
- Secure all apps: Consistently secure all applications used across the enterprise, including modern cloud native apps, legacy private apps and SaaS apps as well as apps that use dynamic ports and those that leverage server-initiated connections.
But that’s not all ZTNA 2.0 solutions can offer organizations.
Single Unified Approach with ZTNA 2.0
ZTNA 2.0 solutions provide superior security while delivering uncompromised performance and exceptional user experiences, all from a single unified approach. ZTNA 2.0 provides a truly cloud native architecture built to secure today’s digital enterprises at cloud scale, providing uncompromised performance backed by leading SLAs that deliver exceptional user experiences. Being completely software-based and hardware neutral, ZTNA 2.0 ensures auto scaling to keep up with changing hybrid workforce and evolving business demands without requiring manual interactions or processes.
- Unified Security Product: ZTNA 1.0 solutions require you to manage separate policies across different management consoles to completely secure all users and apps. It is impossible to effectively avoid incidents, or detect and respond to incidents when management, policy and data are scattered across your infrastructure. ZTNA 2.0 offers a unified product across all capabilities including ZTNA, SWG, NG-CASB, FWaaS, DLP and more. It is designed to provide truly unified management, policy and data for all users and apps.
- Deliver Exceptional Performance and Experiences: Current ZTNA 1.0 solutions rely on physical services deployed in rented colocation facilities that are loosely cobbled together, leveraging the public internet as their primary backbone. This approach severely limits the reach, scale and performance of the solution while placing undesired dependency on third-party data centers and suboptimal connections. These solutions also lack true multitenancy to alleviate the challenges of “noisy neighbors” and “fate sharing,” requiring customers to sacrifice security for experience.
To ensure true end-to-end multitenancy, ZTNA 2.0 solutions should provide a dedicated data plane per customer, avoiding “noisy neighbor” issues that ZTNA 1.0 approaches suffer from. What’s more, ZTNA 2.0 should be designed with native digital experience monitoring (DEM) capabilities, providing proactive identification of problems, along with the ability to isolate and resolve issues automatically to ensure the best possible experience.
Learn more about ZTNA 2.0 in this blog.